Edge Architecture¶
Overall Architecture¶
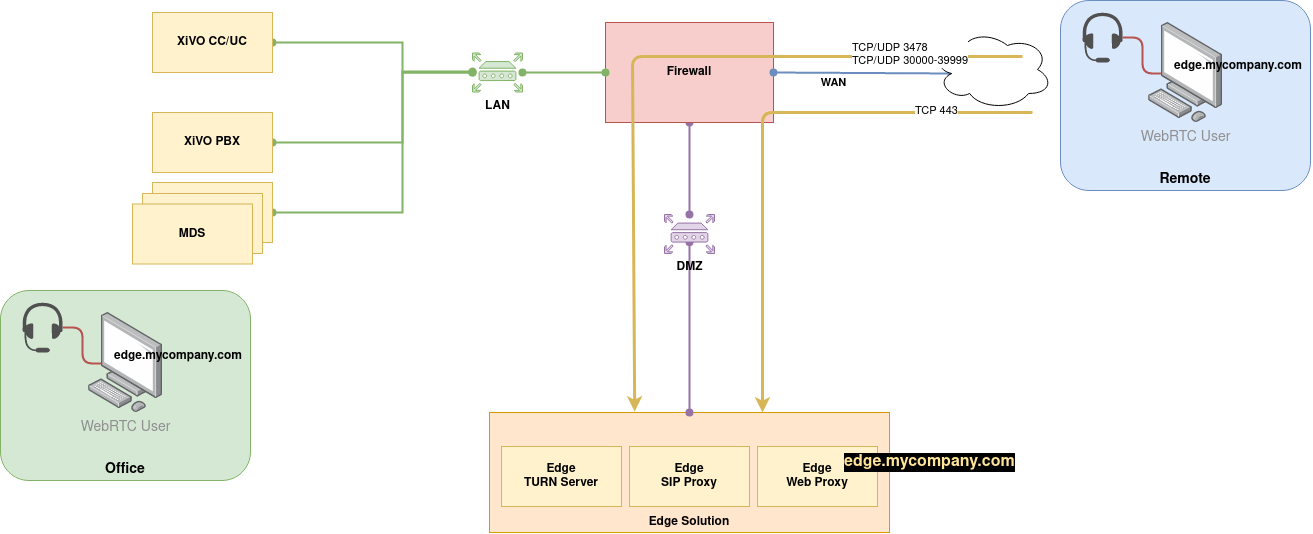
As you can see on the schema above the Edge Solution is to be put inside one’s company DMZ.
From the external world only the Edge Solution will be seen. Only HTTPS and TURN flows should be authorized from the external - see Network Flows for more details.
The Edge Solution is composed of three components:
- a Web Proxy
- a SIP Proxy
- and a TURN Server
These components can be installed:
- on 3 separate servers - see 3 Servers Installation
- or on 1 server - see 1 Server Installation
Network Flows¶
From the outside (WAN to DMZ)¶
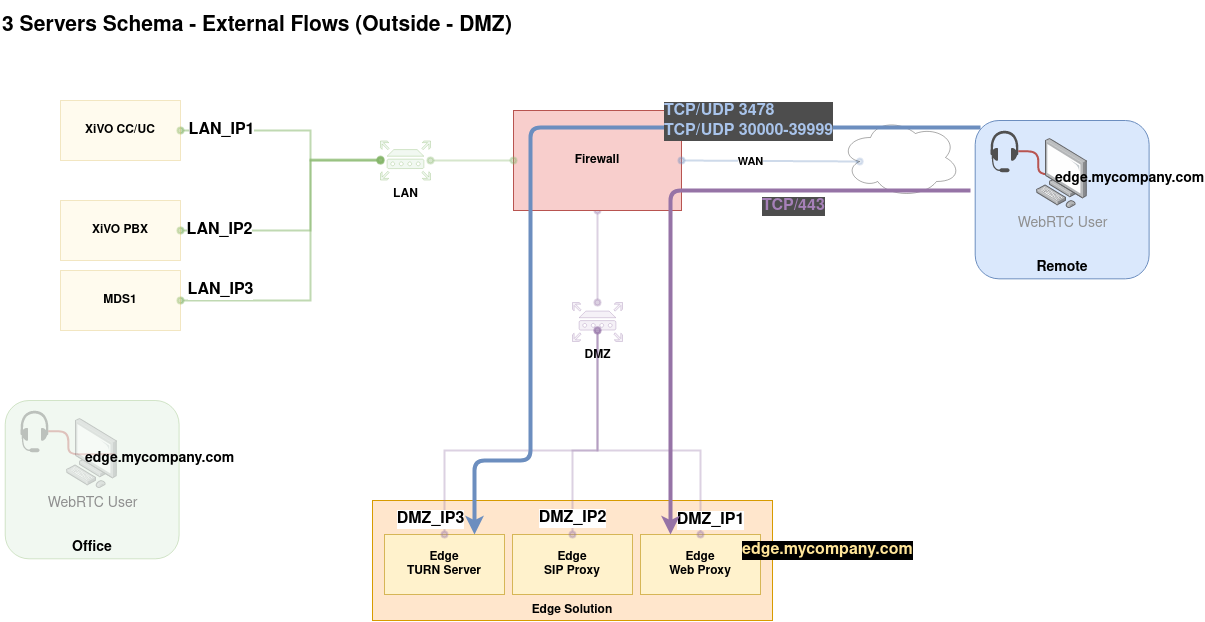
| From | To | Ports to open | Usage |
|---|---|---|---|
Outside
|
Web Proxy
|
|
UC Application from External Users |
Outside
|
TURN Server
|
|
STUN/TURN via UDP, TCP |
Outside
|
TURN Server
|
|
RTP Flow between remote WebRTC client and TURN Server |
Internally (DMZ to LAN)¶
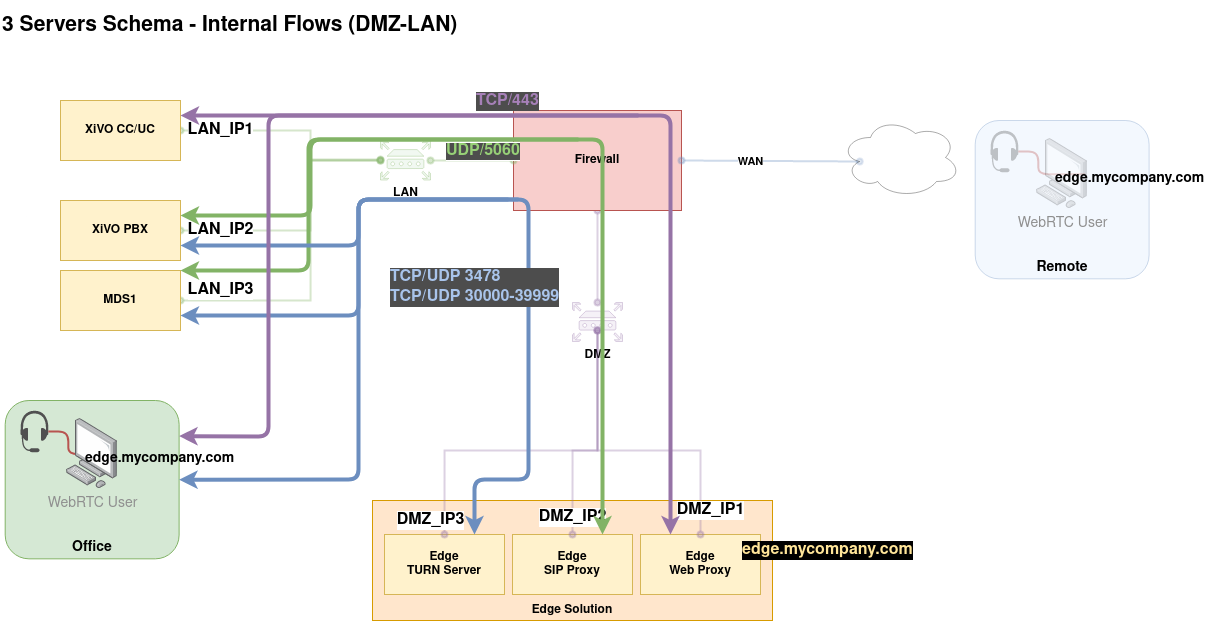
| From/To | To/From | Ports to open | Usage |
|---|---|---|---|
Web Proxy
|
XiVO CC
|
|
Proxified UC application from Edge towards CC/UC Server |
Web Proxy
|
UC Clients
|
|
UC Application for Internal Users |
TURN Server
|
Mediaservers (inc. Main)
|
|
STUN/TURN request between Asterisk and TURN Server |
TURN Server
|
Mediaservers (inc. Main)
|
|
RTP Flow between Asterisk and TURN Server (when using TURN) |
SIP Proxy
|
Mediaservers (inc. main)
|
|
SIP flow between Asterisk(s) and SIP Proxy |
Access for internal clients towards Edge servers (LAN to DMZ):
| From | To | Ports to open | Usage |
|---|---|---|---|
UC Clients
|
Web Proxy
|
|
UC Application for Internal Users |
UC Clients
|
TURN Server
|
|
STUN/TURN request between UC Clients and TURN Server |
Inside DMZ¶
| From/To | To/From | Ports to open | Usage |
|---|---|---|---|
Web Proxy
|
SIP Proxy
|
|
Websocket for SIP |
This is probably unneeded (traffic between servers inside the DMZ should be in most of the cases unfiltered), but if it would be the case this flow must be authorized.